Cybersecurity Pivoting in Penetration Testing: A Practical Guide to Accessing Networks Securely | EC-Council

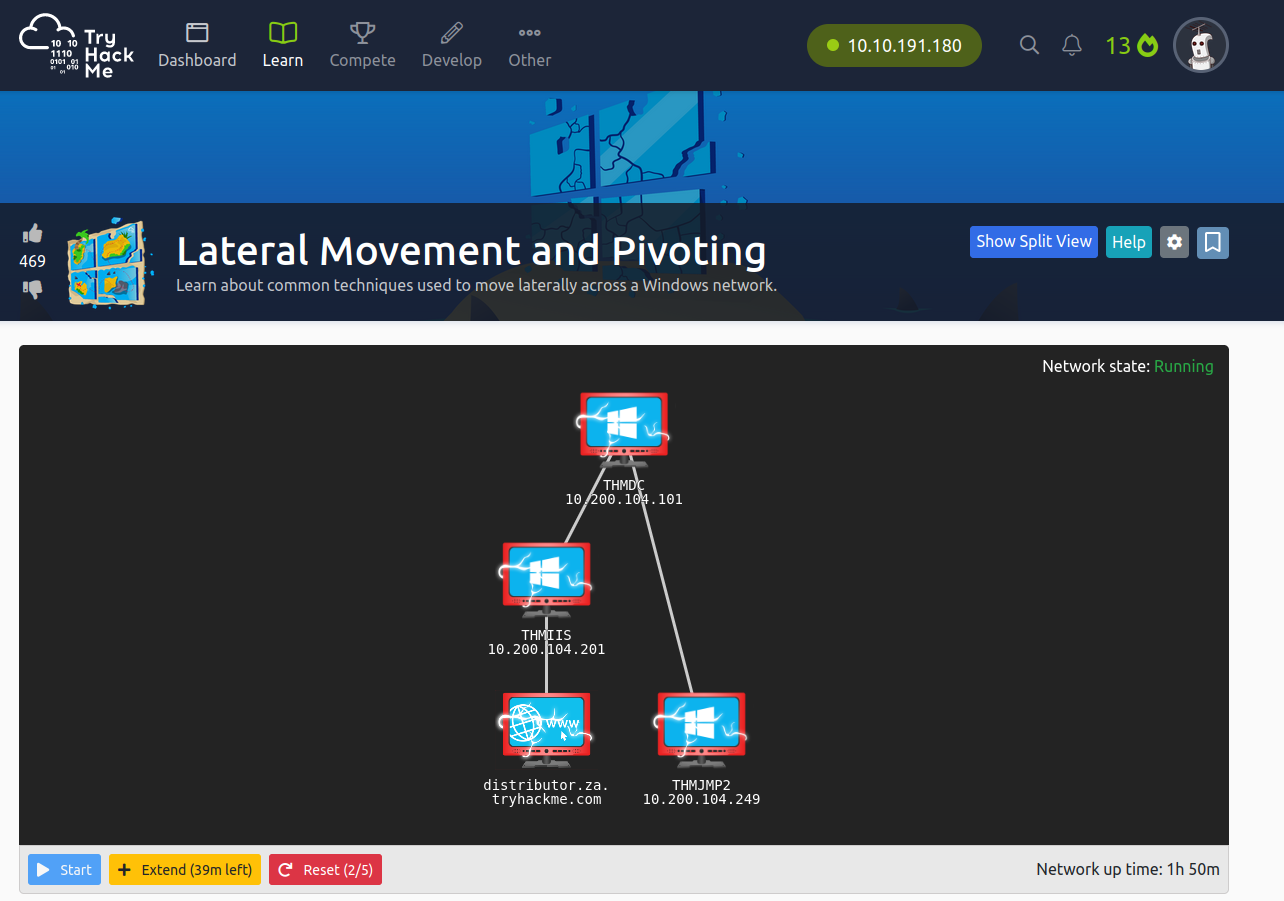
TryHackMe on X: "NEW RED TEAM MODULE: Post-Compromise! Secure your initial foothold & prepare your next steps after gaining access to your target network! 🔴Enumeration 🔴Abusing Windows, Priv Esc & Local Persistence



![[PRACTICAL]Let's Do Lateral Movement And Pivoting[HINDI] - YouTube [PRACTICAL]Let's Do Lateral Movement And Pivoting[HINDI] - YouTube](https://i.ytimg.com/vi/9lT5cQxCXVU/hqdefault.jpg?v=608d344c)






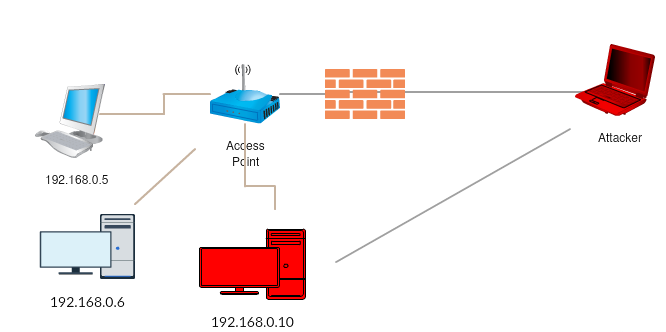
![Overview of network pivoting and tunneling [2023 updated] | Rawsec Overview of network pivoting and tunneling [2023 updated] | Rawsec](https://blog.raw.pm/images/pivoting/network1b.png)